Other Examples
We have seen a few examples of Monoalphabetic Substitution Ciphers, and those we have seen are all very important in the development of Cryptography as a subject. However, there are many more that have appeared through history, and in this section we are going to briefly look at three of these.
Morse Code
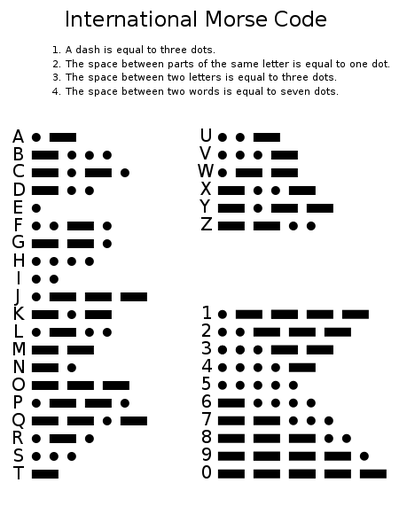
One of the most famous examples of a cipher in regular use is Morse Code (which is not a code, but rather a cipher). Morse Code has the benefit that it can be transmitted in several ways, such as written, by sound or by light. Each letter is replaced by a series of dots and dashes as given by the key below.
One of the most famous examples of a cipher in regular use is Morse Code (which is not a code, but rather a cipher). Morse Code has the benefit that it can be transmitted in several ways, such as written, by sound or by light. Each letter is replaced by a series of dots and dashes as given by the key below.
The brilliance of the Morse Code system is that it can also be transmitted as an audio signal, and was originally used to send messages via telegraph (before telephones had been invented). In this form, each dot is given by a short beep, and a dash by a longer beep (three times the length of a dot). There are various other rules as shown in the key above regarding the length of gaps and other things in transmission.
Morse code has played a pivotal role in the development of technology, specifically telecommunication. Although not secure, since the key is widely known, it is still an interesting use of ciphers in the world today (many boats and planes still use Morse Code to communicate in bad weather when voices sounds crackly), and most importantly, the development of the Code went hand in hand with other technological discoveries (a story which we shall see repeats often in the history of Cryptography).
The Babington Plot
As with the long history of Cryptography, there is an ongoing battle between the cryptographer and the cryptanalysist. The war follows the same pattern every time: the code-makers design a new code, more secure than the last, and start using it to transfer secret messages; meanwhile the code-breakers try to find methods to break this new code, and when they do they use this to their advantage to gather information; the code-makers become aware that their code has been broken, and the process starts all over again.
As with the long history of Cryptography, there is an ongoing battle between the cryptographer and the cryptanalysist. The war follows the same pattern every time: the code-makers design a new code, more secure than the last, and start using it to transfer secret messages; meanwhile the code-breakers try to find methods to break this new code, and when they do they use this to their advantage to gather information; the code-makers become aware that their code has been broken, and the process starts all over again.
There are few examples of this which resound in history quite as strongly as the story behind Mary, Queen of Scots.
The truth behind the execution of Mary is a thick plot, involving many conspirators and a great deal of cryptography. It all starts with the imprisonment of Mary by her cousin, Queen Elizabeth I. Mary was kept imprisoned for over 20 years, and during this time, there were many plots to release her.
The reason for this was that Mary was a figure head for the Catholic Church in England, and there were many Catholics, both English and foreign, who wished to replace the Protestant Queen Elizabeth with the more preferable Mary. The Privy Council of Elizabeth I were aware of this constant danger, and Sir Francis Walsingham set about a plan to implicate Mary in an assassination plot against the Queen, which would lead to Mary's execution, and would destroy the threat from the Catholics in England.
Walsingham got his opportunity in 1585 (17 years after Mary's imprisonment), when a Catholic exile named Gilbert Gifford was arrested, and convinced to act as a double agent.
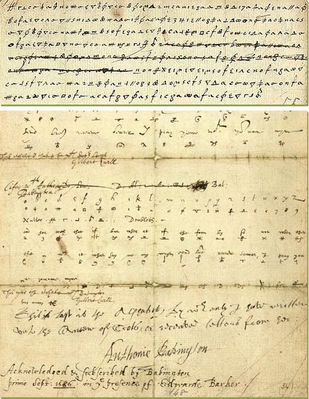
Gifford acted as the delivery person for messages between Mary and the conspirators in a plot to assassinate Elizabeth I. Gifford would collect any messages from the conspirators, and deliver them to Walsingham, who would pass them on to Thomas Phelippes. Now, even though the messages had been intercepted, they were still safe, since the conspirators and Mary were using a cipher to keep the messages secret. However, for a man like Phelippes, the cipher used was elementary and he could easily decipher the message and take a copy. The original would then be passed back to Gifford, who would pass it on to Mary, with nobody any the wiser. The same procedure was followed on the return journey with messages sent from Mary to the conspirators.
Although this continued for a couple of years, Walsingham was waiting for a letter that would incriminate Mary in the plot. In July 1986, the lead conspirator sent a message to Mary detailing the plot. And on July 17, Mary replied. Finally Walsingham had enough proof to convict Mary of conspiracy to assassinate Elizabeth I, but this was not enough for him. He had Phelippes, who was also an excellent forger, add a postscript to the original message, asking for the names of all the conspirators, claiming that she (Mary) wanted to know there names so she could reward them when the deed was done.
Arrests followed quickly, and within 2 months 14 conspirators had been executed, including Babington. On 8 February 1587, Mary, Queen of Scots, was executed by beheading.
This real-life example of ciphers being used shows two main things. The first is that ciphers have been used throughout history to keep secret messages safe. The second, is that as long as there has been the need to keep secret messages, there have been men able to break them, and use the information they find to their advantage, just as Phelippes and Walsingham did.
The Adventure of the Dancing Men
Another example of uses of ciphers is taken not from history, but popular culture. It comes in the form of a Sherlock Holmes Story, written by Sir Arthur Conan Doyle.
Another example of uses of ciphers is taken not from history, but popular culture. It comes in the form of a Sherlock Holmes Story, written by Sir Arthur Conan Doyle.
In this example, Sherlock Holmes is called in to help solve a mystery surrounding a piece of paper with strange stick figures on it. He uses his ingenious to both crack the code, and to send a message to the killer using his own code to entice him to come to the scene, unknowing that the message was written by Holmes.