Transposing Fractionated Ciphertext
As previously discussed, the real power of fractionation methods is when they are combined with other cipher methods, such as transposition. When this is done, the fractionation has the effect of splitting individual letters into 2 components, whilst the transposition then mixes the components up, effectively jumbling up the nature of the letters of the plaintext, not just the order of the letters.
This is an incredibly effective, yet still relatively simple to use mechanism, and adds a great deal of security. The methods can be used with either the Polybius Square or the Straddling Checkerboard, and then the transposition can be any of those methods we have seen.
Encryption
The encryption process relies on the two ciphers we choose (a fractionation and a transposition cipher). We shall look at two examples, to go through some of the different possible combinations.
The encryption process relies on the two ciphers we choose (a fractionation and a transposition cipher). We shall look at two examples, to go through some of the different possible combinations.
|
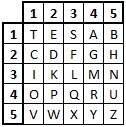
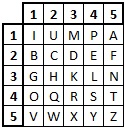
First, we shall look at the plaintext "a simple example", using the keyword test. We shall use the Polybius Square, with Columnar Transposition. The first thing we need to do is to create the Polybius Grid in the usual way with the keyword.
|
|
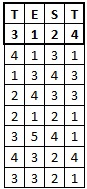
From this, we read off the digit form of the plaintext as our intermediate step. Doing so in this case, we get "41 311343243321 21354143243321". With this, we put this string of digits into the Columnar Transpostion grid, under the keyword test. Doing this, gives us the table on the left.
|
From this we read off a new set of digits, obtaining "1341533 3432422 4122343 1331141", by going down each column in the order specified by the keyword. Finally, we use the Polybius Grid to convert this string of digits back to text.
Doing so gives us a final ciphertext of "IANLMPDADQSLTA".
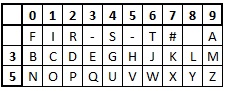
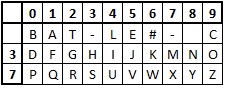
In the second example, we shall use the Straddling Checkerboard, and the Permutation Cipher to encrypt the plaintext "to err is human to forgive divine", this time using the keyword first for the Checkerboard (with key numbers 3 and 5), and second for the permutation.
Again, we start by generating the fractionating grid, this time using the keyword first, and the straddling checkerboard. We get the grid shown, and this gives the intermediate digit step of "651833228148355439950865180512341553383215515033".
|
With this generated, we now need to place the digit string into the permutation grid, as shown to the right, and we read off the next step from here. We obtain "135386 882412 595343 055689 028151 134553 358123 531305".
At this stage we notice that the very last digit is "5", which cannot be encrypted as a single digit using the Straddling Checkerboard. To get round this we could leave it as a digit, but this would not work in the decryption process, as the recipient would insert a numeric escape character for the digit, thus changing the text.
|
The way around this is to signify the problem with a character, and then add an extra digit after the "5". The activity uses "^" to signify this situation, and in decoding, if this is seen, the recipient knows to ignore the very last digit. Doing this gets us "135386 882412 595343 055689 028151 134553 358123 53130^50".
And finally, we put this into the Straddling Checkerboard, to reveal the ciphertext of "IHLT RSIRZQSBVT AFR IOIGVEYIRHCB^N".
Decryption
To decrypt a ciphertext, we must first use the correct fractionation method to get a string of digits. This is then transposed according to the transposition cipher, and finally, the reordered digits are converted back to text using the fractionation board. We shall again look at two examples.
To decrypt a ciphertext, we must first use the correct fractionation method to get a string of digits. This is then transposed according to the transposition cipher, and finally, the reordered digits are converted back to text using the fractionation board. We shall again look at two examples.
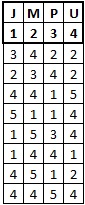
We shall decrypt the ciphertext "RCHESVAOVROPYBST" which has been encoded using th Polybius Square and Permutation Cipher, with a single keyword of jump.
|
We now write out this string of digits in order in a grid of width 4, with the columns numbered 1 to 4, and the letters of the keyword put in alphabetical order (ie jmpu), as shown to the left.
We then shuffle the columns around until the keyword is spelt correctly. This is shown on the right. We then read off the digits in rows from this grid to get
"32422234454154111453114442514445". |
Finally we use this and the Polybius Square to retrieve the plaintext, which reads "decryption is easy".
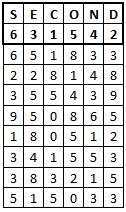
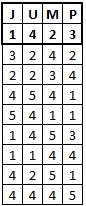
For the second example, we shall use the Straddling Checkerboard with Myszkowski Transposition. We shall use the keyword battle for the Straddling Checkerboard, and war for the transposition. The key numbers for the checkerboard are 3 and 7, and the ciphertext is "TC XTF0AA2L^D". Firstly, we need to add some numeric escape characters to this, to get "TC XTF#0AA#2L^D"
|
We start by generating the checkerboard, and using this to convert the ciphertext into digits. Doing so gets us "2988772316011624^30", but the "^" at the end indicates we need to ignore the final "0", which gives a complete string of "29887723160116243".
|
|
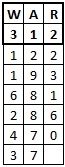
Now we set out a blank grid with the transposition keyword at the top. Since the ciphertext is 17 characters long, and the keyword is 3 letters long, we need 6 rows in our grid. We fill the columns in one at a time, in the numerical order of the letters of the keyword. We get the completed grid to the right.
|
Now we read of the digits by row to get "12219368128647037", and this is decoded using the checkerboard.
The final plaintext is thus "attack at #4pm", or without the numeric escape "attack at 4pm".
Discussion
As discussed earlier, fractionation is an excellent step to make a less secure transposition cipher much harder to break. The process is not overly complicated, and it is definitely still usable with paper and pen methods.
As discussed earlier, fractionation is an excellent step to make a less secure transposition cipher much harder to break. The process is not overly complicated, and it is definitely still usable with paper and pen methods.
The ciphertext does not resemble the plaintext at all, and frequency analysis is of no use, since individual letters are not being substituted. Similarly, anagramming is no help in breaking the code, as it was not the letters that were transposed, but rather their "parts".
Since these ciphers are made up of combining two other ciphers, there are many possible ways to adjust them. We could use a Polybius Square that was a different size (although it must remain a square in this case, otherwise we cannot turn the string of digits back into the ciphertext), or indeed a larger checkerboard. We could change the alphabet and change which letters are combined. We could also include nulls in the transposition, and even use multiple transpositions.