Combining Monoalphabetic and Simple Transposition Ciphers
Both Monoalphabetic Substitution Ciphers and Simple Transposition Ciphers are susceptible to different means of cryptanalysis, and neither has been secure for quite some time. Even more so, with the invention of the computer, these types of codes have fallen, and are not used for any truly important pieces of information.
However, by combining them, we can take the strengths of both systems, and dramatically reduce the weaknesses of either. A piece of ciphertext that has been encrypted with both of these simple ciphers would not have the letter frequencies equal to the native language and so be susceptible to Anagramming (as a transposition cipher has), but when Frequency Analysis is attempted, the letters are in no coherent order, so spotting words and digraphs is also not possible (as it is for simple substitution ciphers).
The best way to combine these two systems is to use the Mixed Alphabet Cipher, alongside the Columnar Transposition Cipher or the Myszkowski Transposition Cipher. To do this we use either a single keyword for both, or two keywords, and perform one cipher after the other. It does not matter which order they are performed, but it is usually easier to do the transposition first, and substitute at the end.
Encryption
To encrypt a message using both the Mixed Alphabet and Columnar Transposition ciphers, we start by using our keyword to generate the transposition grid. Once thie is done, and we have read down the columns in the correct order, we generate our ciphertext alphabet, and substitue each plaintext letter for the appropriate ciphertext letter.
To encrypt a message using both the Mixed Alphabet and Columnar Transposition ciphers, we start by using our keyword to generate the transposition grid. Once thie is done, and we have read down the columns in the correct order, we generate our ciphertext alphabet, and substitue each plaintext letter for the appropriate ciphertext letter.
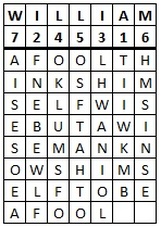
As an example we shall encrypt the plaintext "a fool thinks himself wise, but a wise man knows himself to be a fool", and we shall use the keyword william. We start by making up our grid for the Columnar Transposition.
|
This grid is then read off, down the columns to get the first step in the encryption process: "TIIWK MBFNE BEWLF LHWAN IOLOK LUMSF OOSFT AHTOH MSINS EAISE SOEA".
If you are unsure how we got to this result, then look back at Columnar Transposition.
|
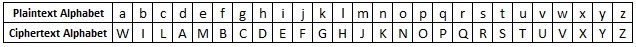
Next we must generate the ciphertext alphabet using the keyword william.
With this, we now substitute each letter in the middle step with the appropriate ciphertext letter. For example, "a" is replaced with "W". For more information see Mixed Alphabet Cipher. After this step we get the final ciphertext:
SEEVG JIBKM IMVHB HDVWK ENHNG HTJRB NNRBS WDSND JREKR MWERM RNMW
Decryption
The decryption process when using two ciphers combined is to take it one step at a time. First undo the substitution using the ciphertext alphabet. Once this is done, you must then reorder the letters using the transposition grid. These individual processes are identical to the decryption techniques we saw in Mixed Alphabet Ciphers and Columnar Transposition.
The decryption process when using two ciphers combined is to take it one step at a time. First undo the substitution using the ciphertext alphabet. Once this is done, you must then reorder the letters using the transposition grid. These individual processes are identical to the decryption techniques we saw in Mixed Alphabet Ciphers and Columnar Transposition.
Discussion
You could use any of the Monoalphabetic Substitution Ciphers combined with any one of the Simple Transposition Ciphers. The reason that I have chosed the two that I did, was that they are the most secure of each type, and by combining them, we achieve maximum security for these types.
You could use any of the Monoalphabetic Substitution Ciphers combined with any one of the Simple Transposition Ciphers. The reason that I have chosed the two that I did, was that they are the most secure of each type, and by combining them, we achieve maximum security for these types.
This combined approach, though fairly simple to implement, is actually very secure. This is one instance where the total is far greater than the sum of its parts. However, with computers, and even before, messages written using this method could still be cracked using elements of frequency analysis and anagramming together.
To achieve even better results, we shall have to combine transposition ciphers with fractionating methods such as the Polybius Square or Straddling Checkerboard. But for the hobbiest, or somebody needing to keep a little thing hidden, this method would provide an almighty task to an inexperienced cryptanalyst.